Your Amazon Driver Just Did a Better Penetration Test Than Your IT Company
I nearly spat my tea across the room.
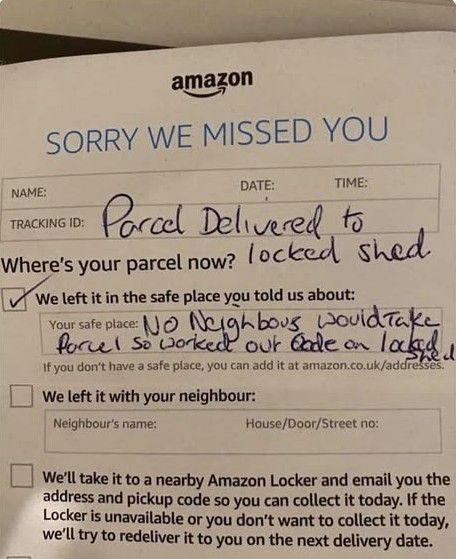
A friend sent me a photo this week of an Amazon delivery note. You may have seen it doing the rounds. It reads, and I am quoting directly here: "Parcel Delivered to locked shed. No neighbours would take parcel so worked out code on locked shed."
He worked out the code. On a locked shed. And then left a note to let you know.
I have been in cybersecurity for the better part of three decades. I have read thousands of penetration test reports. I have never, not once, seen a findings document this concise, this honest, or this cheerfully unaware of itself.
Pull up a chair, because this humble Amazon delivery note just taught you everything you need to know about physical security, default credentials, trusted third parties, and why "compliance theatre" will get you absolutely nowhere.
The World's Most Accidental Penetration Tester
Let us look at what actually happened here, because it is worth unpacking properly.
An authorised third party arrived at a premises with a legitimate business purpose. Standard stuff. He could not complete his primary objective through normal channels. Nobody was home. Neighbours declined. So he assessed the environment, identified an alternative access point, applied some lateral thinking to overcome the access control protecting it, gained entry, completed his objective, and then filed a written disclosure report explaining precisely how he did it.
That is a penetration test. That is textbook penetration test methodology. The only difference between this delivery driver and a firm charging you £5,000 a day is the high-vis jacket and the fact that he left a Jiffy bag instead of a 47-page PDF full of RAG-rated findings.
He even ticked the compliance checkbox on the form. "We left it in the safe place you told us about." Technically accurate. Operationally terrifying.
This is compliance theatre in its purest, most beautiful form.
"Worked Out the Code." Three Words That Should Keep You Awake.
Here is the bit that matters. He did not force the lock. He did not cut through the door. He worked out the code.
How do people work out codes? Let me count the ways.
They try the obvious ones first. 1234. 0000. The year the owner was born, helpfully displayed on a Facebook profile.
The house number.
The last four digits of a phone number, written on the key fob hanging next to the shed key inside the house, which is itself protected by a Yale lock manufactured in 1987.
They look for contextual clues. What numbers mean something to this person? What is written nearby? What is the most likely thing someone who "just needs a quick code for the shed" would choose?
They try the factory default. Because an absolutely staggering number of people never change it.
Does any of this sound familiar? It should. Because this is precisely how attackers get into your systems. They do not kick the door down. They try "admin/admin."
They check whether the router still has the default password printed on the label. They look at your LinkedIn profile to find out your dog is called Biscuit and then try Biscuit2024 on your email account.
The delivery driver did not break your security. You never had any.
The Trusted Third Party Problem
There is a second lesson buried in this note, and it is arguably more important for your business than the password one.
The delivery driver was trusted. He was authorised to be on your property. You gave him implicit permission to leave parcels in safe places by setting up a safe place preference on your Amazon account. You probably did not think very hard about what "safe place" meant in practice, because you were busy, and it seemed like a minor administrative task, and Amazon made it very easy to just click "yes, my shed" and move on.
And now a stranger knows the code to your locked outbuilding.
This is the supply chain trust problem in miniature. Every time you grant a third party access to some part of your world, whether that is your IT systems, your premises, your cloud environment, or your locked shed, you are making an assumption about how far that trust extends and what they will do with it. Most of the time, the assumption is reasonable. People are, in general, trying to do the right thing.
But the delivery driver who worked out your shed code with good intentions is functionally identical to the one who worked it out with bad intentions. The code does not know the difference. The access is the same. The outcome depends entirely on the character of the person holding it.
Your IT systems cannot tell the difference either. When an MSP engineer logs into your network using a compromised credential, your firewall sees an authorised connection. When a North Korean IT contractor sitting in Pyongyang logs into your company laptop using the identity you hired them under, your HR system sees an employee doing their job. The problem of insider threats and compromised trusted access is not theoretical.
He Left the Vulnerability Report Where Anyone Could Find It
Now here is the part that made me actually laugh out loud, because it is so perfectly, exquisitely awful.
He documented the breach.
He wrote down, in his own handwriting, on a piece of paper now sitting on your doormat or shoved through your letterbox, that he had worked out the code to your locked shed. He described the method. He described the outcome. He confirmed that access was achieved.
This note is now available to every subsequent visitor to your property. The postman. The window cleaner. The person who knocks on your door trying to sell you roof insulation. Anyone who happens to pick it up off your doormat before you get home.
He left a written guide to bypassing your physical security control sitting in your front porch.
I genuinely cannot think of a better physical-world analogy for what happens when organisations store sensitive security information carelessly. Passwords in a shared spreadsheet. System architecture diagrams emailed to the wrong distribution list. VPN credentials in a Teams chat that never gets cleaned up. The information exists. Someone wrote it down. It ended up somewhere it should not be.
The delivery driver is not the villain of this story. He was being helpful. But the information he left behind is a risk regardless of his intentions. Careless handling of access information is a data breach waiting to happen.
Your Shed Is Not the Point. Your Business Is.
Right. Let us move from the genuinely funny to the actually concerning, because everything I have just described about the shed applies directly to your business premises and your IT systems.
Walk around your office and count how many access controls exist that have never been properly tested. The door code that has not changed since you moved in. The Wi-Fi password written on a Post-it note stuck to the reception desk. The alarm code that is the same as the safe combination because "it's easier to remember." The meeting room booking system with the default admin password. The NAS drive in the back office that nobody has touched since 2019.
Now ask yourself: if a well-intentioned Amazon driver could work out your shed code in the time it takes to deliver a parcel, how long would a motivated attacker spend on your front door?
The NCSC's guidance on physical security is clear, and it applies to codes and combinations just as much as it applies to locks and barriers: access controls are only effective if they are not predictable. "Worked out the code" is a polite way of saying "defeated the access control." The fact that the person doing it was trying to help is irrelevant to the risk.
What This Means for Your Business: Five Things to Do This Week
1. Audit every code and combination you use. Shed, office door, safe, alarm, gate. If any of them is a date, a number sequence, a house number, or something that has not been changed since it was set up, change it today. Not this month. Today.
2. Catalogue your trusted third parties. Who has access to your premises? Who has access to your systems? Do you have a list? When did you last review it? Do your cleaning contractors, IT support team, delivery preferences, and cloud service accounts actually need the access they have, or did you just never bother to review it?
3. Stop writing access information down in accessible places. This includes Post-it notes, shared documents with no access controls, emails with "password" in the subject line, and Teams messages that sit in channels anyone in the company can read. If your credentials are poorly managed, you are already compromised.
4. Think about what your "compliance checkbox" actually covers. The driver ticked the box that said he had left the parcel in a safe place. He had. The box said nothing about whether the safe place was actually safe. Your Cyber Essentials certification works the same way. It is a point-in-time snapshot that says your controls met a minimum standard on the day of the assessment. It does not say they are working today, or that your users have not done something creative since then.
5. Consider getting an actual penetration test done. I realise this is a slightly awkward segue after spending 1,500 words praising an Amazon driver, but the point stands. If you do not know how someone would get into your systems or your premises, you are guessing. A proper penetration test tells you. Unlike the delivery driver, a professional will not leave the findings on your doormat.
Now Make This Work For You
This is actually a gift, if you use it right.
Physical and digital security theatre is rampant in UK small businesses. Codes that have not changed in five years, access rights that have never been reviewed, trusted third parties with more access than they need. Most of your competitors are in exactly this position, and most of them are not thinking about it.
Businesses that take access control seriously have fewer incidents, lower insurance premiums, and more credibility with enterprise clients who are increasingly scrutinising their supply chains. If your business can demonstrate documented access control reviews, regular credential rotation, and a clear third-party access policy, you are ahead of 80% of the market.
Use this story. Seriously. Tell it in your next client pitch. Tell it to your team at the next staff meeting. It is funny, it is memorable, and it makes a complicated security concept immediately, viscerally understandable. The best security training is the kind people actually remember. Nobody forgets the Amazon driver who cracked the shed.
If you are an IT manager or security lead trying to get budget for a physical security review, an access control audit, or a penetration test, this story is your opening slide. No, seriously.
The financial risk argument: A compromised access control, whether physical or digital, can result in theft, data breach, and ICO enforcement action. The average cost of a UK SMB data breach in 2024 was over £10,000, and that figure does not include reputational damage or lost contracts.
The compliance argument: GDPR requires appropriate technical and organisational measures to protect personal data. "Organisational measures" includes physical access controls. If your office has weak physical security and personal data is accessible on-site, you have a compliance exposure. The ICO has issued fines for exactly this type of failing.
The supply chain argument: If you handle data for larger clients or operate in regulated sectors, your clients are increasingly requiring you to demonstrate access control policies. Enterprise clients are tightening their supply chain security requirements. Being unable to produce evidence of a review is a deal-breaker.
The simplest argument of all: Show them the photo of the note. Watch the penny drop. Then ask for the budget.
| Source | Article |
|---|---|
| NCSC | Physical Security Guidance |
| NCSC | Password Administration for System Owners |
| NCSC | Supply Chain Security Guidance |
| NCSC | 10 Steps to Cyber Security: Access Control |
| ICO | A Guide to Data Security |
| ICO | Personal Data Breaches: A Guide |
| CREST | What Is Penetration Testing? |
| DSIT / DCMS | Cyber Security Breaches Survey 2025 |
| NCSC | Third Party and Supply Chain Cyber Security |
| Cyber Essentials | Cyber Essentials Scheme Overview |