When Enforcement Gets Teeth: UK Case Studies in Accountability That Works
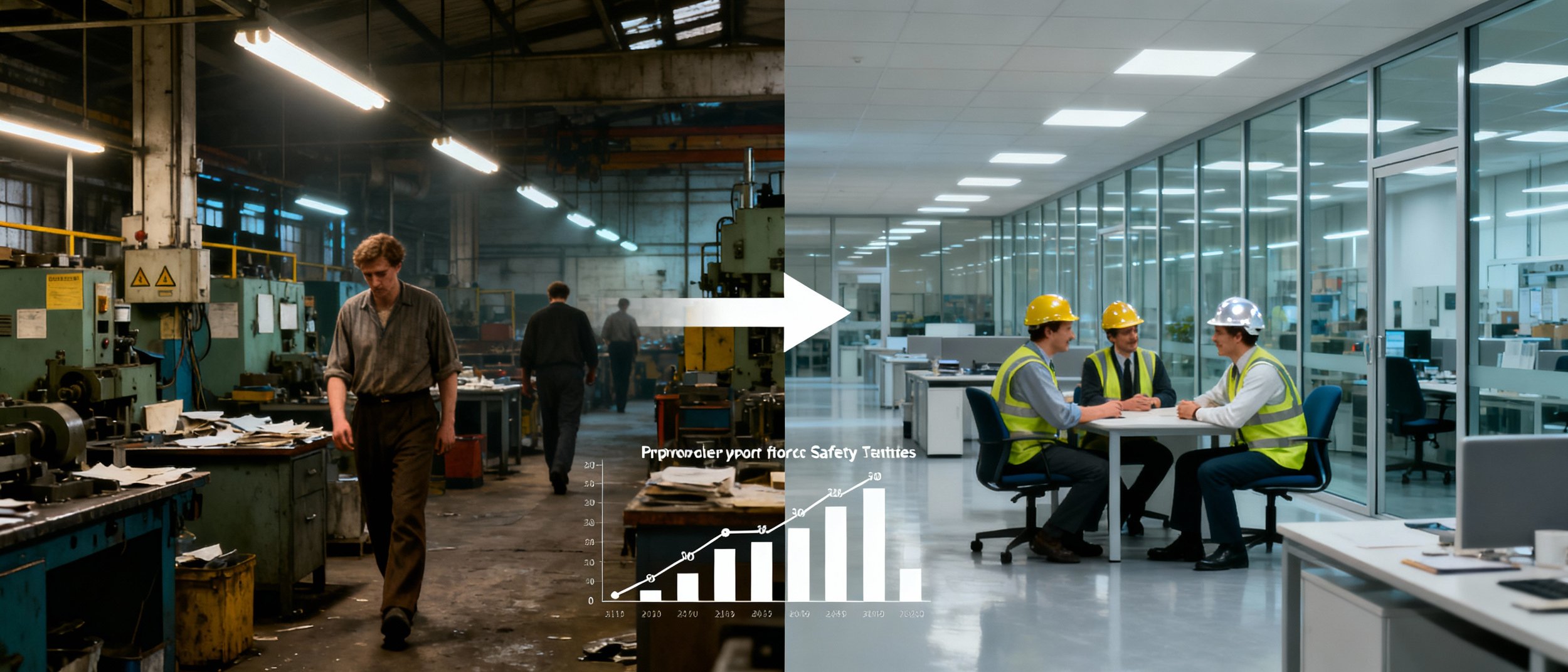
In 1981, 495 workers died in British workplaces.
In the most recent figures, that number is 124.
A 75% reduction over four decades. But the transformation didn't happen gradually through natural progress. It happened because regulations got teeth and directors faced real consequences.
Today: What HSE enforcement actually achieved, how it achieved it, and what cybersecurity enforcement could accomplish using the same principles.
The HSE Transformation Story
The Health and Safety at Work Act 1974 created the framework. But frameworks without enforcement are just paperwork.
What actually changed behaviour:
1. Personal Prosecution of Directors
Before: Companies paid fines. Directors remained insulated. Safety was someone else's problem.
After: Directors faced criminal courts. Prison sentences became possible. Criminal records followed convicted executives into future employment.
The psychological shift was immediate. When the first construction director went to prison for negligent safety practices, every construction company director in Britain suddenly found budget for safety improvements.
2. Inspector Powers That Mattered
HSE inspectors gained authority to:
Enter any workplace without notice
Issue immediate prohibition notices stopping dangerous work
Seize equipment and documents as evidence
Require information under penalty of law
Refer cases directly to prosecution
This wasn't advisory guidance. This was enforcement with consequences.
3. Outcome-Based Testing
HSE doesn't just check paperwork. Inspectors test whether safety measures actually work.
Scaffolding documented as installed? Let's go look at it. Safety training documented as completed? Let's quiz workers. Emergency procedures documented? Let's run a drill.
The gap between documentation and reality became prosecutable.
The Numbers That Prove It Works
Fatal Injuries to Workers in Great Britain:
1981: 495 deaths
1990s average: approximately 250 deaths annually
2010s average: approximately 140 deaths annually
2024/25: 124 deaths
Rate per 100,000 workers:
1981: Approximately 2.0
Current: Approximately 0.4
This is an 80% reduction in fatality rate, even as the workforce grew and industries evolved.
Prosecution Statistics:
HSE prosecutes between 400-600 cases annually. Conviction rates exceed 90%. Fines totalling approximately £73 million are levied each year.
But the real impact isn't fines. It's behaviour change driven by prosecution risk.
The Construction Industry Case Study
Construction remains one of Britain's most dangerous industries. Yet even here, transformation is evident.
Before HSE Enforcement:
Falls from height were accepted industry hazards. Hard hats were optional. Safety training was minimal. Workers who complained were replaced.
After Sustained Enforcement:
Falls from height reduced by over 60% since systematic enforcement began
Hard hats and personal protective equipment became universal
Safety certification became standard for site work
Companies compete partly on safety records
The mechanism: Every major construction company knows directors have been prosecuted. That knowledge shapes every safety decision.
What Cybersecurity Enforcement Could Achieve
If ICO enforcement followed HSE principles, what might we expect?
Conservative Projection (Based on HSE's First Decade)
HSE achieved approximately 30% reduction in workplace fatalities within its first decade of proper enforcement.
Applied to data breaches affecting over 10,000 records:
2024 baseline: Approximately 1,000 significant breaches annually
After 10 years of HSE-style enforcement: Approximately 700 annually
That's 300 fewer catastrophic data breaches per year. Millions of people whose personal information stays protected.
Optimistic Projection (Based on HSE's 40-Year Achievement)
Full 85% reduction would mean approximately 150 significant breaches annually from the current 1,000.
This sounds ambitious, but cybersecurity has advantages workplace safety lacked:
Technical controls are more standardised
Implementation is often faster than physical safety changes
The threat landscape creates strong business incentives beyond regulation
Most Likely Outcome
Based on comparable international implementations (Singapore, EU NIS2 preparations), a 50-60% reduction in preventable breaches within 15 years of proper enforcement seems achievable.
"Preventable" being the key word. Sophisticated nation-state attacks won't disappear. But breaches caused by default passwords, missing MFA, and unpatched systems could decline dramatically.
The Cost-Benefit Reality
HSE's Economic Impact:
The estimated cost of workplace injuries and new cases of work-related ill health currently runs approximately £22.9 billion annually. Without HSE's 50 years of enforcement, this figure would be dramatically higher.
Investment in HSE enforcement generates estimated returns of £10-20 for every £1 spent on prevention.
Projected Cybersecurity Enforcement Economics:
Current UK cyber crime costs are estimated at £27 billion annually. Even a modest 20% reduction through enforcement would save approximately £5.4 billion per year.
ICO enforcement budget would need to increase from approximately £70 million to perhaps £200-300 million for proper technical capability.
The return on investment is obvious. £200 million spent to save £5 billion represents 25:1 returns.
Why Current ICO Enforcement Fails
The contrast with HSE is instructive.
HSE Enforcement:
400-600 prosecutions annually
£73 million in fines collected
Personal director liability standard
Technical inspectors test actual conditions
Prohibition notices stop dangerous work immediately
ICO Enforcement:
Fewer than 50 enforcement actions annually resulting in fines
Approximately £2.7 million in fines collected (before recent increases)
No personal director liability
Limited technical testing capability
Advisory notices rather than prohibition powers
The disparity is structural, not accidental. ICO was designed for data protection advice, not enforcement. Transformation requires fundamental restructuring.
International Comparisons
Singapore Cybersecurity Act 2018
Singapore introduced comprehensive cybersecurity legislation including:
Personal liability provisions for officers
Mandatory breach notification
Sector-specific regulations for critical infrastructure
Technical auditing requirements
While specific breach reduction statistics vary by sector, Singapore's regulatory approach is widely regarded as significantly strengthening cybersecurity posture across regulated industries.
EU NIS2 Directive
Coming into full force across EU member states, NIS2 introduces:
Direct management liability for cybersecurity
Mandatory security requirements for essential entities
Cross-border enforcement cooperation
Significant administrative fines
The UK is not leading this transformation. We're behind international peers.
Australia's Security of Critical Infrastructure Act
Australia implemented:
Mandatory reporting of cyber incidents
Positive security obligations
Government assistance powers for serious incidents
Personal liability provisions being developed
The Industry Transformation Pattern
Based on HSE's experience, enforcement-driven transformation follows predictable phases.
Phase 1: Resistance (Years 1-2)
Industry lobbying against "excessive regulation." Claims of unworkability and competitive disadvantage. Media stories about businesses closing due to compliance costs.
Phase 2: Adaptation (Years 3-5)
First prosecutions establish precedent. Companies realise compliance is cheaper than prosecution. Security investment increases across affected sectors.
Phase 3: Normalisation (Years 5-10)
New businesses enter market expecting security requirements. Compliance costs decline through competition and standardisation. Security becomes normal business practice rather than special effort.
Phase 4: Institutionalisation (Years 10+)
The next generation cannot imagine operating without proper security. Standards become universal baseline. Focus shifts to continuous improvement rather than basic compliance.
HSE's timeline took approximately 20 years to reach Phase 4. Cybersecurity could move faster given the established model.
The Human Cost of Inaction
Behind breach statistics are real people.
The Synnovis Attack (2024): A ransomware attack on the NHS pathology provider directly contributed to patient deaths through delayed diagnoses and disrupted treatment. The human cost of cybersecurity failure is no longer theoretical.
Identity Theft Victims: Each major breach creates thousands of identity theft victims. Financial losses, credit damage, emotional distress, and years of remediation.
Business Destruction: 60% of small businesses that suffer significant cyber attacks cease trading within six months. The owners, employees, and families affected by preventable breaches deserve better protection.
HSE enforcement wasn't popular initially. But nobody argues that 370 fewer annual workplace deaths is wrong.
What Needs to Happen
Based on HSE's successful model:
1. Legislative Change
New primary legislation creating personal director liability for cybersecurity negligence, proportionate to business size.
2. ICO Transformation
Significant budget increase. Technical enforcement capability. Inspector powers matching HSE's. Prosecution capacity for serious cases.
3. Clear Standards
Cyber Essentials as legal safe harbour for small businesses. Higher standards clearly defined for larger organisations.
4. Gradual Implementation
Multi-year transition allowing businesses to adapt. Large organisations first. SMB protections built into timeline.
5. Support Infrastructure
Government-funded assistance programmes. Training subsidies. Free NCSC resources expanded.
The Political Question
The evidence is clear. HSE-style enforcement works. International examples demonstrate applicability to cybersecurity. The cost-benefit analysis is overwhelmingly positive.
The only remaining question is political will.
Are UK legislators prepared to implement what demonstrably works? Are they willing to face industry lobbying in exchange for dramatically improved national cybersecurity?
The conversation this week has laid out exactly what's possible. The rest is democracy.
Tomorrow: Weekend opinion on why the status quo is no longer acceptable.